Thesis Draft
Author: Yannick Huchard
Date: 29 April 2026
Discipline: Technology Strategy / Information Systems / Enterprise Architecture
Abstract
This thesis develops a technology sourcing and governance decision model that extends the classical build-versus-buy dilemma into a broader, more realistic decision space. In contemporary enterprises, technology leaders no longer choose only between internal development and external acquisition. They also decide whether to rent capabilities as services, partner for co-development, reuse existing assets, compose modular ecosystems, or accelerate implementation through AI-assisted engineering. Existing frameworks often remain binary, heuristic, or narrowly cost-centric, making them insufficient for digital, regulated, and innovation-intensive environments. This thesis proposes a multi-layer decision model that separates governance alternatives from implementation modes. Governance alternatives include Build, Buy, Rent, and Partner. Implementation modes include Reuse, Compose, Generate, and conventional custom development. The model evaluates alternatives across nine dimensions: strategic value, internal capability, externalization capability, technology maturity and accessibility, economic attractiveness, control/compliance/sovereignty, risk exposure, flexibility/reversibility, and option value under uncertainty. The thesis integrates transaction cost economics, the resource-based view, dynamic capabilities, real options reasoning, and multicriteria decision-making into one coherent framework. It argues that technology sourcing should be treated not merely as a procurement or engineering choice, but as a capital allocation decision over future capabilities, control positions, learning trajectories, and strategic optionality. In addition to the conceptual model, the thesis provides a scoring system, gating rules, measurement constructs, and an empirical validation design suitable for expert calibration and multi-case analysis.
Keywords: technology sourcing; build versus buy; IT outsourcing; governance; dynamic capabilities; real options; platform strategy; multicriteria decision-making.
Chapter 1. Introduction
The build-versus-buy decision has long been one of the most persistent questions in technology management. In its classical form, the dilemma appears simple: should an organization develop a capability internally or obtain it through the market? That formulation remains useful as a starting point, yet it no longer captures the full reality of contemporary technology governance.
Modern enterprises operate in a decision space shaped by cloud platforms, modular ecosystems, software-as-a-service, platform-as-a-service, open-source infrastructure, strategic partnerships, managed services, and AI-assisted engineering. In this environment, leaders do not decide only whether to build or buy. They decide what they must control, what they should learn, what can remain reversible, what can be standardized, and what should become part of the organization’s enduring capability base.
The central argument of this thesis is that technology sourcing decisions should be understood as governance choices over future capability ownership, dependence, learning, optionality, and value capture. A sourcing decision does not only determine how a capability will be obtained. It determines what the firm will know, what it will govern, what it will outsource, what it can later change, and where it will sit in a broader ecosystem of technology providers and partners.
This thesis therefore proposes a multi-layer technology sourcing and governance decision model. The model extends the traditional binary by introducing four governance alternatives—Build, Buy, Rent, and Partner—and by treating Reuse, Compose, Generate, and Custom Develop as implementation modes that can exist across those governance forms. The resulting framework is intended to be both theoretically grounded and practically usable.
The work contributes in four main ways. First, it updates the conceptual vocabulary of sourcing. Second, it separates governance choice from implementation logic. Third, it makes flexibility and reversibility central rather than secondary. Fourth, it provides a research-ready operational structure capable of calibration, testing, and application in executive decision contexts.
1.1 Research Problem
Organizations increasingly make technology sourcing decisions under strategic pressure, regulatory constraint, technological turbulence, and uneven internal capability. Yet the frameworks used to guide those decisions often remain narrow, local, and heuristic. Many organizations still rely on informal judgments, isolated business cases, or cost-led reasoning that underweights control, risk, learning, and optionality.
The research problem addressed in this thesis is therefore the lack of an integrated, rigorous, and operationally usable model for selecting among modern technology sourcing and governance alternatives.
1.2 Research Question and Objectives
The core research question is: how should organizations evaluate and choose among Build, Buy, Rent, and Partner alternatives when sourcing technology capabilities under strategic, economic, regulatory, and uncertainty constraints?
- reconceptualize build-versus-buy as a broader technology sourcing and governance problem;
- distinguish governance alternatives from implementation modes;
- identify the constructs that materially shape sourcing decisions;
- operationalize those constructs into a scoring and decision model;
- define a robust empirical validation pathway for the proposed model.
Chapter 2. Literature Review
2.1 Scope of the Review
This literature review draws from five major streams: make-or-buy and boundary-of-the-firm theory, information systems outsourcing, the resource-based view and dynamic capabilities, real options reasoning, and multicriteria decision-making. The purpose of the review is not merely to summarize these streams, but to show why none of them, in isolation, fully explains the modern sourcing decision.
The review demonstrates that technology sourcing is now a hybrid problem. It is simultaneously a governance problem, a strategic capability problem, a risk problem, a flexibility problem, and a decision-structuring problem. This multi-dimensionality explains why a more integrated model is necessary.
2.2 Historical Evolution of Make-or-Buy
The make-or-buy question originates in the broader economic problem of firm boundaries. Coase explained the existence of firms through the comparative costs of using markets versus organizing activities internally. Williamson later expanded this logic by emphasizing transaction costs, asset specificity, uncertainty, and governance hazards.
In operations and manufacturing, make-or-buy was associated with cost structures, quality control, supply dependence, and vertical integration. In strategic management, it became linked to the protection of core competences and the preservation of competitive advantage. In information systems, the problem evolved into decisions over outsourcing, application development, infrastructure management, and technology services.
What has changed most in recent decades is not simply the number of sourcing options, but the nature of what is being sourced. Organizations now source embedded expertise, operational maturity, innovation velocity, elasticity, compliance support, ecosystem access, and in some cases signaling value through association with technology leaders. This widening of the sourced object is central to the present thesis.
The information systems outsourcing literature provides the most direct foundation for this thesis. It has shown that outsourcing decisions are shaped not only by cost, but also by strategic importance, measurement difficulty, skill availability, governance quality, partnership structures, and outcome uncertainty.
Dibbern and colleagues demonstrated that IS outsourcing research had already become a complex, multi-stage field involving decision, transition, governance, and outcome phases. Later reviews by Lacity, Khan, Willcocks, and others further clarified that the field could not be explained by a single theory and that outsourcing outcomes depended strongly on client capability, vendor governance, and contextual factors.
This literature is especially important because it makes clear that externalization is not passive. Successful buying, renting, or partnering requires organizational ability to specify, select, negotiate, integrate, govern, monitor, and exit external arrangements. That insight directly informs the construct of Procurement and Externalization Capability in this thesis.
2.4 Transaction Cost Economics
Transaction cost economics remains one of the most influential foundations for sourcing research. It explains governance choices by comparing the hazards and costs associated with market exchange and internal coordination. Asset specificity, uncertainty, measurement difficulty, and opportunism are central variables.
In technology contexts, transaction cost economics is highly relevant whenever a capability is difficult to contract for completely, highly interdependent with internal processes, subject to future adaptation, or exposed to significant dependency risk. It helps explain why some capabilities should remain internal even when external markets appear efficient.
At the same time, transaction cost economics is limited when the sourcing decision is driven by learning, strategic differentiation, or long-term capability accumulation rather than purely governance efficiency. This is one reason why the present thesis integrates it with other perspectives.
2.5 Resource-Based View and Dynamic Capabilities
The resource-based view shifts attention from governance hazards to value creation. It suggests that firms should protect and cultivate resources and capabilities that are valuable, rare, difficult to imitate, and difficult to substitute. In technology management, this implies that some software, data, orchestration, and algorithmic capabilities should not be treated as ordinary procurement items.
Dynamic capabilities extend this perspective by emphasizing the capacity to sense opportunities, seize them, and reconfigure assets over time. This is highly relevant for sourcing because the attractiveness of Build, Buy, Rent, or Partner is rarely stable. Technology standards mature, providers change, regulatory conditions evolve, and internal capabilities improve or decay.
Together, these perspectives support two key ideas in the thesis: first, strategic value and knowledge accumulation matter materially to sourcing; second, sourcing decisions must include reassessment logic rather than assuming permanent optimality.
2.6 Real Options and Decision Structuring
Real options reasoning contributes the idea that flexibility has economic value. Under uncertainty, the ability to defer, stage, switch, expand, contract, or exit may be worth more than apparent short-term cost advantages. This logic is especially important in fast-moving domains such as AI, cloud services, and digital platforms.
The multicriteria decision-making literature contributes methodologically. It demonstrates that heterogeneous criteria can be structured, weighted, and compared systematically rather than left to informal executive judgment alone. Approaches such as AHP and TOPSIS are especially relevant because they make trade-offs explicit while still allowing hard constraints to override compensatory scoring.
Taken together, the literature points toward a sourcing model that must be multi-theoretical, multi-layered, and operationally explicit. That is the role of the model developed in this thesis.
Chapter 3. Theoretical Foundations and Research Gap
3.1 Integrated Theoretical Position
This thesis adopts an explicitly integrative theoretical position. Transaction cost economics explains governance hazards and dependency. The resource-based view explains strategic value and the protection of capability advantage. Dynamic capabilities explain reassessment, adaptation, and reconfiguration. Real options explain the value of reversibility and delayed commitment. Multicriteria decision-making explains how such dimensions can be structured into a usable decision artifact.
The research gap emerges from the fact that existing frameworks either remain too binary, too heuristic, or too fragmented across these theoretical traditions. Many models explain part of the sourcing problem well, but few integrate the full modern decision space in a structured way.
3.2 Identified Gaps
- the dominant vocabulary remains too narrow: Build and Buy are no longer sufficient to describe the decision space;
- governance choice and implementation logic are often conflated;
- flexibility, reversibility, and option value remain under-modeled;
- externalization capability is rarely treated as a strategic organizational capability in its own right;
- dynamic reassessment is insufficiently represented in most sourcing frameworks.
The thesis responds to these gaps by proposing a multi-layer technology sourcing and governance decision model that is conceptually clear, empirically operationalizable, and directly relevant to executive technology governance.
Chapter 4. Conceptual Model Development
4.1 Model Architecture
The proposed model is structured in four layers: a pre-decision layer, a strategic qualification layer, an evaluation layer, and a decision-and-reassessment layer.
The pre-decision layer asks whether the problem requires a fresh sourcing decision at all. It applies a reuse-first logic and checks whether the requirement can be met through governed extension of existing assets.
The strategic qualification layer classifies the capability according to strategic profile and lifecycle profile. The evaluation layer scores the capability across the core constructs of the model. The decision layer applies gating rules, calculates alternative utilities, ranks governance alternatives, and specifies future reassessment triggers.
4.2 Governance Alternatives
Build
the organization develops and retains primary governance over the capability, including architecture, prioritization, and often operations.
Buy
the organization acquires a product or licensed solution as the core source of the capability.
Rent
the organization accesses the capability as a service, subscription, utility, or managed operational arrangement.
Partner
the organization co-develops, co-governs, or strategically aligns with an external actor in a more relational form than ordinary procurement.
4.3 Implementation Modes
Reuse
leveraging existing internal or governed external assets before creating or sourcing anew.
Compose
assembling the capability from modular services, APIs, or components.
Generate
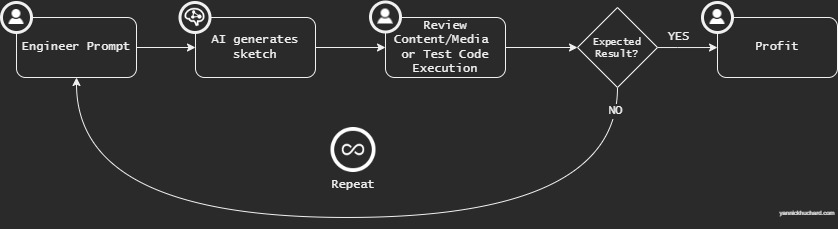
using AI-assisted software engineering or agentic development to accelerate creation, integration, or adaptation.
Custom Develop
bespoke development without strong dependence on an existing governed base.
4.4 Strategic and Lifecycle Qualification
The model classifies capabilities by strategic profile: Commodity, Differentiating, Core, or Disruptive. Commodity capabilities typically bias toward Buy or Rent. Core and Disruptive capabilities increase the relative attractiveness of Build or carefully governed Partner arrangements.
Capabilities are also classified by lifecycle profile: Disposable, Transitional, or Enduring. Disposable capabilities may rationally privilege speed and optionality. Enduring capabilities require stronger attention to evolvability, control, and long-term operating logic.
P1. Higher Strategic Value increases the relative attractiveness of Build and strategically aligned Partner arrangements.
P2. Higher Internal Capability increases the feasibility and attractiveness of Build.
P3. Higher Procurement and Externalization Capability increases the attractiveness of Buy, Rent, and Partner.
P4. Higher Technology Maturity and Accessibility increases the attractiveness of Buy and Rent.
P5. Higher Control, Compliance, and Sovereignty requirements increase the attractiveness of Build and constrained Partner structures.
P6. Higher Risk Exposure decreases the attractiveness of the affected option.
P7. Higher Flexibility and Reversibility increase the attractiveness of Rent and many Partner arrangements.
P8. Higher Option Value under uncertainty increases the attractiveness of Rent and, in some cases, Partner.
P9. Greater Reuse Availability reduces the likelihood of Build-from-scratch across all governance forms.
P10. The relationship between Strategic Value and preferred governance alternative is moderated by Internal Capability, Technology Maturity, and Control requirements.
Chapter 5. Construct Definitions and Operationalization
This chapter formalizes the constructs that support the model. The intent is to make the framework research-ready and decision-ready. Not all variables are treated as reflective latent constructs. Several are better modeled as composite indices built from heterogeneous but decision-relevant components.
Strategic Value
Definition: the extent to which a capability contributes to competitive advantage, differentiation, innovation potential, and valuable knowledge accumulation.
Indicative dimensions: Core Strategic Relevance; Differentiation Contribution; Innovation Potential; Knowledge Accumulation Value.
Expected directional effect: higher levels generally strengthen the attractiveness of Build and Partner.
Internal Capability
Definition: the organization’s ability to design, build, deliver, govern, and operate the capability internally over time.
Indicative dimensions: Engineering Expertise; Domain Expertise; Delivery Maturity; Human Bandwidth; Operational Capability.
Expected directional effect: higher levels generally strengthen the attractiveness of Build.
Procurement and Externalization Capability
Definition: the organization’s ability to identify, assess, contract, integrate, govern, monitor, and exit external sourcing arrangements.
Indicative dimensions: RFP Maturity; Contracting Capability; Vendor Governance; SLA Management; Integration Capability; Exit Management Capability.
Expected directional effect: higher levels generally strengthen the attractiveness of Buy, Rent, and Partner.
Technology Maturity and Accessibility
Definition: the degree to which the technology domain is standardized, tooled, supported, and practically accessible.
Indicative dimensions: Standards Maturity; Tooling Maturity; Talent Availability; Ecosystem Maturity; Technology Accessibility.
Expected directional effect: higher levels generally strengthen the attractiveness of Buy and Rent, and secondarily Build feasibility.
Economic Attractiveness
Definition: the overall economic desirability of an alternative across initial cost, medium-term cost, change cost, and time-to-value.
Indicative dimensions: Initial Cost Attractiveness; TCO Attractiveness; Cost of Evolution Attractiveness; Time-to-Value Attractiveness.
Expected directional effect: higher levels generally strengthen the attractiveness of Context dependent.
Control, Compliance, and Sovereignty
Definition: the degree to which the capability requires internal authority over roadmap, operations, data, compliance execution, and jurisdictional assurance.
Indicative dimensions: Data Sensitivity; Regulatory Burden; Roadmap Control Need; Operational Control Need; Sovereignty Requirement.
Expected directional effect: higher levels generally strengthen the attractiveness of Build and constrained Partner.
Risk Exposure
Definition: the level of vulnerability associated with a governance option, including vendor, geopolitical, cyber, legal, dependency, and immaturity risk.
Indicative dimensions: Vendor Fragility; Geopolitical Risk; Security Risk; Legal/Compliance Risk; Dependency Risk; Immaturity/Beta Risk.
Expected directional effect: higher levels generally strengthen the attractiveness of Penalizes the exposed option.
Flexibility and Reversibility
Definition: the degree to which the arrangement allows adaptation, switching, scaling, exit, or reconfiguration without excessive disruption.
Indicative dimensions: Ease of Exit; Portability; Modularity; Switching Cost Attractiveness; Scalability Elasticity; Update Velocity.
Expected directional effect: higher levels generally strengthen the attractiveness of Rent and Partner.
Option Value
Definition: the strategic and economic value of preserving future choice under uncertainty.
Indicative dimensions: Technology Uncertainty; Demand Uncertainty; Innovation Velocity; Exit/Change Strategic Value.
Expected directional effect: higher levels generally strengthen the attractiveness of Rent and selected Partner arrangements.
Collaboration Fit
Definition: the extent to which a co-development or co-governance arrangement is strategically, operationally, and relationally viable.
Indicative dimensions: Co-development Willingness; Strategic Alignment; Shared Governance Feasibility; Acceptability of Value and IP Sharing.
Expected directional effect: higher levels generally strengthen the attractiveness of Partner.
5.1 Measurement and Normalization
Judgment-based items are measured on a 1–7 Likert-type scale and normalized to a 0–100 scale. Objective variables such as cost or expected implementation duration can also be normalized to 0–100 through a desirability or min–max transformation.
The generic normalization formula for 1–7 items is shown below.
xₙ = ((x − 1) / 6) × 100
Dimension scores are calculated as arithmetic means unless a context-specific weighting of sub-dimensions is explicitly justified.
5.2 Contextual Variables
The model also includes contextual variables that influence interpretation and gating: Strategic Profile, Lifecycle Profile, Time Criticality, Mandatory Sovereignty Constraint, Reuse Availability, Trigger Exposure, and Brand Leverage Potential.
Chapter 6. Scoring Model and Decision Logic
6.1 Pre-Decision Rule
The model begins with a mandatory principle: Reuse before Try before Build, Buy, Rent, or Partner. If a reusable governed asset already satisfies the need above a defined threshold, the decision should be reframed around reuse or extension before greenfield sourcing is considered.
6.2 Gating Rules
- If sovereignty is mandatory and an external arrangement cannot satisfy jurisdictional requirements, the incompatible Rent or Buy option is disqualified.
- If internal capability is below a minimum threshold and time criticality is extreme, Build may be disqualified.
- If vendor fragility, geopolitical exposure, or compliance incompatibility exceed tolerance, the affected external option is disqualified.
- If lifecycle intent is disposable and strategic value is low, heavy Build should generally be discouraged unless explicit learning value is high.
6.3 Illustrative Utility Logic
Build Utility
U(Build) = 0.24·SVS + 0.22·ICS + 0.16·CCSS + 0.10·TMAS + 0.08·FRS + 0.10·(100−PECS) + 0.10·(100−EASext)
Buy Utility
U(Buy) = 0.18·(100−SVS) + 0.18·PECS + 0.15·TMAS + 0.20·EAS + 0.10·(100−CCSS) + 0.10·(100−RES) + 0.09·FRS
Rent Utility
U(Rent) = 0.14·PECS + 0.14·TMAS + 0.16·EAS + 0.18·FRS + 0.18·OVS + 0.10·(100−CCSS) + 0.10·(100−RES)
Partner Utility
U(Partner) = 0.20·SVS + 0.10·ICS + 0.18·PECS + 0.12·TMAS + 0.10·EAS + 0.12·FRS + 0.18·CFS
These utility functions are thesis-draft formulas intended for calibration rather than universal fixed weights. In a full empirical phase, weights should be calibrated through AHP or a comparable structured expert procedure.
6.4 Decision Outputs
- primary recommendation;
- secondary recommendation;
- disqualified alternatives and reasons;
- dominant decision drivers;
- confidence score based on the gap between the top two options;
- robustness score based on sensitivity analysis;
- review interval and reassessment triggers.
Chapter 7. Research Methodology
This thesis adopts a pragmatic, abductive, and design-oriented methodology. It combines conceptual theory building with the design of a decision artifact and a future empirical validation pathway. A purely positivist approach would be too narrow because several constructs depend on structured executive judgment. A purely interpretivist approach would be insufficient because the thesis aims to produce a formalizable, reproducible decision model.
The methodology is therefore hybrid. It starts from theory, learns from practical decision realities, and culminates in an artifact capable of calibration and testing. This is appropriate for a problem that is simultaneously explanatory, normative, and decision-support oriented.
7.1 Research Design
- Phase 1: conceptual development of the model from literature synthesis and structured practitioner reasoning;
- Phase 2: construct refinement and content validation through expert review and Delphi-style convergence;
- Phase 3: weight calibration using AHP and structured pairwise comparison;
- Phase 4: empirical application and validation using retrospective and comparative sourcing cases.
7.2 Unit of Analysis
The primary unit of analysis is the technology capability sourcing decision. This may be a customer identity platform, fraud engine, claims workflow, reporting engine, pricing engine, AI assistant, integration layer, or other bounded capability. This unit is appropriate because sourcing decisions are often made at capability level and may differ materially within the same organization.
7.3 Measurement Design
The model combines objective indicators, structured ratings, composite indices, and contextual qualifiers. Content validity is strengthened through literature grounding and expert review. Because multiple evaluators may apply the model to the same case, inter-rater reliability and evaluator training are important.
7.4 Validation Logic
A full empirical validation should include content validity, face validity, inter-rater consistency, sensitivity analysis, and multiple-case comparison. The model’s recommendation should be compared not only with historical decisions, but also with observed post-decision outcomes, because a mismatch may indicate that the original organizational choice was itself weak.
Chapter 8. Empirical Validation Design
The empirical validation design is phased and cumulative. It begins with expert validation of constructs and decision logic, proceeds to weight calibration, and culminates in case-based application and cross-case comparison.
The purpose of validation is not only to confirm plausibility, but to assess whether the model can be understood, applied consistently, calibrated transparently, and used meaningfully in real sourcing contexts.
8.1 Expert Validation
A panel of CTOs, CIOs, enterprise architects, procurement leaders, risk officers, and senior delivery or engineering leaders should assess construct completeness, terminology clarity, missing dimensions, and gating logic.
8.2 AHP Weight Calibration
Pairwise comparisons across the major criteria should be used to derive context-aware weights and consistency ratios. Subgroup comparison may reveal meaningful differences between technology, procurement, and risk leadership populations.
8.3 Case-Based Validation
The model should be applied to a theoretically sampled set of historical sourcing cases covering successful and unsuccessful Build, Buy, Rent, and Partner decisions. Each case should document the capability, context, alternatives considered, actual choice, and observed outcomes.
8.4 Evaluation Metrics
- recommendation plausibility;
- alignment with historical decision;
- consistency with observed outcomes;
- inter-rater reliability;
- robustness under changed weights or uncertain inputs;
- managerial usefulness in governance discussions.
Chapter 9. Discussion
This thesis suggests that technology sourcing should be treated as a structured decision over future capability ownership, control, adaptability, and learning. It is not simply an argument about cost minimization or engineering preference.
The model also highlights that sourcing decisions are path-dependent. Every Build decision develops internal muscles. Every Buy or Rent decision develops—or fails to develop—externalization muscles such as procurement maturity, vendor governance, and integration discipline. Every Partner decision shapes the firm’s relationship to ecosystem dependence, collaborative learning, and shared control.
From this perspective, sourcing is a portfolio discipline. It requires explicit choices about what the firm wants to own intellectually, what it wants to own operationally, what it wants to accelerate externally, and what it wants to keep reversible.
Chapter 10. Contributions
10.1 Theoretical Contributions
The thesis extends classical boundary-of-the-firm reasoning into a contemporary technology governance context by formalizing Build, Buy, Rent, and Partner as distinct governance alternatives. It also integrates transaction cost economics, the resource-based view, dynamic capabilities, real options, and multicriteria decision-making into one coherent decision architecture.
A further theoretical contribution is the reframing of sourcing as capability capital allocation. Each sourcing decision is treated as an investment in future knowledge, control, dependence, optionality, and organizational muscle formation rather than merely as a choice of delivery mechanism.
10.2 Conceptual Contributions
One of the strongest conceptual contributions is the explicit separation between governance alternatives and implementation modes. This distinction resolves a persistent confusion in both practice and prior frameworks.
The thesis also contributes a layered decision logic that combines reuse-first reasoning, strategic qualification, construct-based evaluation, non-compensatory gating, utility scoring, and dynamic reassessment.
10.3 Methodological and Managerial Contributions
The thesis translates a strategic managerial debate into a research-ready model with formal constructs, scoring logic, utility functions, decision outputs, and validation pathways.
For practitioners, it offers a more mature executive language for technology investment. It recognizes that buying and renting also require capability, and it gives organizations a structure for governing sourcing decisions with greater transparency and repeatability.
Chapter 11. Limitations
The model is intentionally broad, which increases relevance but also creates abstraction. A framework capable of spanning software platforms, cloud services, ecosystems, and AI-assisted delivery cannot capture every domain-specific nuance without contextual tailoring.
The thesis also integrates multiple theoretical traditions that do not share identical assumptions. This is a strength from a design perspective, but it means the work contributes more to theory integration and decision architecture than to isolated extension of any single theory.
Several constructs remain partly judgment-based. Strategic Value, Collaboration Fit, and Option Value can be structured rigorously, but they cannot be reduced to purely objective measures. Weighting also remains context-sensitive, which means calibration matters materially.
Finally, the manuscript provides a strong empirical validation design but not yet the full executed validation at scale. The thesis is therefore conceptually strong and methodologically ready, but its predictive and comparative performance still requires systematic empirical testing.
Chapter 12. Conclusion
This thesis began from the observation that the classical build-versus-buy framing no longer captures the full reality of contemporary technology sourcing. Modern organizations operate in a richer and more volatile decision space shaped by platform ecosystems, service models, modular architecture, regulation, and AI-assisted software creation.
The thesis responded by proposing a multi-layer technology sourcing and governance decision model that distinguishes governance alternatives from implementation modes, embeds sourcing decisions in capability and control logic, and treats flexibility and optionality as central rather than peripheral variables.
The work has argued that sourcing decisions should be understood as decisions over strategic possibility. A Build decision may create long-term control and learning. A Buy decision may secure speed and embedded expertise. A Rent decision may preserve elasticity and option value. A Partner decision may accelerate innovation while sharing risk and governance. None of these options is inherently superior in the abstract; each becomes more or less attractive depending on strategic value, capability maturity, uncertainty, control need, and risk.
The enduring contribution of the thesis is therefore not only the model itself. It is the invitation to treat technology sourcing as a serious discipline of strategic governance under uncertainty.
References
Alaghehband, F. K., Rivard, S., Wu, S., & Goyette, S. (2011). An assessment of the use of transaction cost theory in information technology outsourcing. The Journal of Strategic Information Systems, 20(2), 125–138.
Aubert, B. A., Rivard, S., & Patry, M. (1996). A transaction cost approach to outsourcing behavior. Information & Management, 30(2), 51–64.
Aubert, B. A., Rivard, S., & Patry, M. (2004). A transaction cost model of IT outsourcing. Information & Management, 41(7), 921–932.
Balliauw, M., Kort, P. M., & Zhang, A. (2021). From theoretical real options to practical decision support: An analysis of the real options approach and its pitfalls for decision-makers. Journal of Economic Dynamics and Control, 129, 104172.
Barney, J. (1991). Firm resources and sustained competitive advantage. Journal of Management, 17(1), 99–120.
Bharadwaj, A. S. (2000). A resource-based perspective on information technology capability and firm performance: An empirical investigation. MIS Quarterly, 24(1), 169–196.
Brewer, B., Ashenbaum, B., & Ogden, J. (2014). Outsourcing the procurement function: Do actions and results align with theory? Journal of Purchasing and Supply Management, 20(2), 94–104.
Coase, R. H. (1937). The nature of the firm. Economica, 4(16), 386–405.
De Giovanni, P. (2018). Capacity investment under uncertainty: The effect of volume flexibility and the value of real options. International Journal of Production Economics, 198, 105–119.
Dibbern, J., Goles, T., Hirschheim, R., & Jayatilaka, B. (2004). Information systems outsourcing: A survey and analysis of the literature. The DATA BASE for Advances in Information Systems, 35(4), 6–102.
Eisenhardt, K. M., & Martin, J. A. (2000). Dynamic capabilities: What are they? Strategic Management Journal, 21(10–11), 1105–1121.
Espino-Rodríguez, T. F., & Padrón-Robaina, V. (2006). A review of outsourcing from the resource-based view of the firm. International Journal of Management Reviews, 8(1), 49–70.
Folta, T. B. (1998). Governance and uncertainty: The trade-off between administrative control and commitment. Strategic Management Journal, 19(11), 1007–1028.
Grover, V., Cheon, M. J., & Teng, J. T. C. (1996). The effect of service quality and partnership on the outsourcing of information systems functions. Journal of Management Information Systems, 12(4), 89–116.
Henderson, J. C., & Venkatraman, N. (1993). Strategic alignment: Leveraging information technology for transforming organizations. IBM Systems Journal, 32(1), 4–16.
Kahraman, C., Engin, O., Kabak, Ö., & Kaya, İ. (2009). Information systems outsourcing decisions using a group decision-making approach. Engineering Applications of Artificial Intelligence, 22(6), 832–841.
Lacity, M. C., Khan, S. A., & Willcocks, L. P. (2009). A review of the IT outsourcing literature: Insights for practice. The Journal of Strategic Information Systems, 18(3), 130–146.
Lacity, M. C., Khan, S. A., Yan, A., & Willcocks, L. P. (2010). A review of the IT outsourcing empirical literature and future research directions. Journal of Information Technology, 25(4), 395–433.
Lacity, M. C., Khan, S. A., Yan, A., & Willcocks, L. P. (2011). Towards an endogenous theory of information technology outsourcing. The Journal of Strategic Information Systems, 20(2), 139–157.
McFarlan, F. W. (1981). Portfolio approach to information systems. Harvard Business Review, 59(5), 142–150.
McIvor, R. (2009). How the transaction cost and resource-based theories of the firm inform outsourcing evaluation. Journal of Operations Management, 27(1), 45–63.
Mikalef, P., & Pateli, A. (2017). Information technology-enabled dynamic capabilities and their indirect effect on competitive performance. Journal of Business Research, 70, 1–16.
Porter, M. E. (1985). Competitive advantage: Creating and sustaining superior performance. Free Press.
Prahalad, C. K., & Hamel, G. (1990). The core competence of the corporation. Harvard Business Review, 68(3), 79–91.
Saaty, T. L. (1980). The analytic hierarchy process. McGraw-Hill.
Sambamurthy, V., Bharadwaj, A., & Grover, V. (2003). Shaping agility through digital options: Reconceptualizing the role of information technology in contemporary firms. MIS Quarterly, 27(2), 237–263.
Teece, D. J. (2007). Explicating dynamic capabilities: The nature and microfoundations of sustainable enterprise performance. Strategic Management Journal, 28(13), 1319–1350.
Teece, D. J., Pisano, G., & Shuen, A. (1997). Dynamic capabilities and strategic management. Strategic Management Journal, 18(7), 509–533.
Tiwana, A. (2014). Platform ecosystems: Aligning architecture, governance, and strategy. Morgan Kaufmann.
Watjatrakul, B. (2005). Determinants of IS sourcing decisions: A comparative study of transaction cost theory versus the resource-based view. The Journal of Strategic Information Systems, 14(4), 389–415.
Wilden, R., Gudergan, S. P., Nielsen, B. B., & Lings, I. (2013). Dynamic capabilities and performance: Strategy, structure and environment. Long Range Planning, 46(1–2), 72–96.
Williamson, O. E. (1975). Markets and hierarchies: Analysis and antitrust implications. Free Press.
Williamson, O. E. (1985). The economic institutions of capitalism. Free Press.
Williamson, O. E. (1991). Comparative economic organization: The analysis of discrete structural alternatives. Administrative Science Quarterly, 36(2), 269–296.
Appendices
Appendix A. Example Measurement Instrument
Strategic Value
Rate each item from 1 (very low) to 7 (very high):
- This capability is central to our long-term strategic positioning.
- This capability contributes materially to market differentiation.
- This capability may enable future innovation or disruption.
- Internal control over this capability would generate valuable learning.
Internal Capability
Rate each item from 1 (very low) to 7 (very high):
- We possess the engineering expertise required for this capability.
- We have the business/domain expertise required.
- Our teams are mature enough to deliver this capability reliably.
- We have sufficient human bandwidth to absorb this work.
- We can operate and evolve this capability after delivery.
Procurement and Externalization Capability
Rate each item from 1 (very low) to 7 (very high):
- We can compare external solutions rigorously.
- We can negotiate robust legal and commercial terms.
- We can govern external providers effectively over time.
- We can integrate external capabilities effectively.
- We can prepare and execute an exit if needed.
Appendix B. Decision Output Template
- Capability name and scope
- Strategic profile and lifecycle profile
- Reuse opportunities identified
- Disqualified alternatives and reasons
- Utility scores for remaining alternatives
- Primary and secondary recommendation
- Key decision drivers and key risks
- Confidence and robustness indicators
- Review interval and reassessment triggers
Appendix C. AHP and Case Validation Templates
TODO: The full empirical version of this thesis should include structured AHP pairwise comparison sheets, Delphi round prompts, case reconstruction templates, evaluator guidance, and sensitivity analysis worksheets.